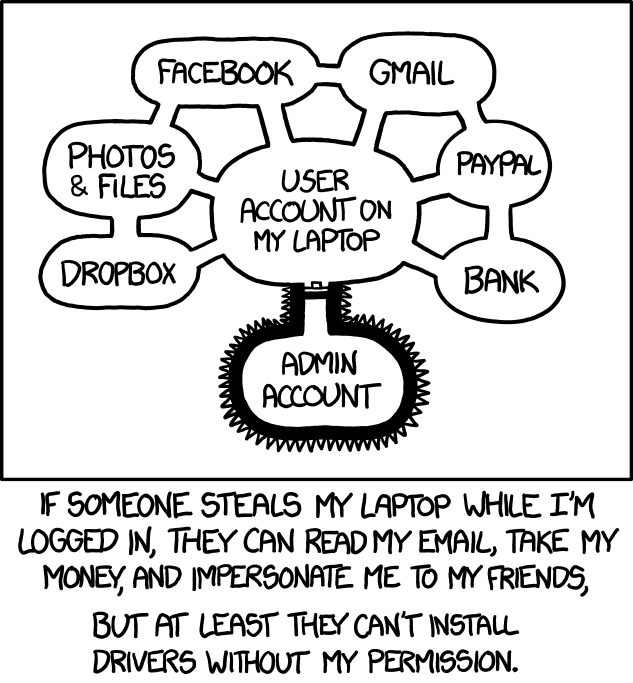
Why does your admin account look like a scrotum?
Yours doesn’t?
Wine automatically running:
And then it starts running because you set up wine with binfmt_misc, only to crash a few seconds later
Remember that time, when it was possible for about 6 years to hack into any Linux system (without drive encryption) which had GRUB by pressing backspace exactly 28 times? Yeah, good old times.
https://www.hmarco.org/bugs/CVE-2015-8370-Grub2-authentication-bypass.html
If the adversary has physical access you are generally pwned either way
Breh. What? I feel naked right now.
Better replace your keyboard everytime you leave it unattended, someone could put a keylogger in it. Don’t forget to check for hidden pinhole cameras around that capture you inputting your passwords. Etc, etc. Those even work against an encrypted drive…
To be fair I rotate hardware and DE so often my drives are wiped nearly monthly. But Jesus this is egregious.
grub’s always been a hack. The first stage in 512 byte boot sector chainloads the second stage in the space between boot sector and the first sectors of first partition. Second stage chainloads the kernel. (This is my primitive gist.)
grub was never made for security, it just exists in a place where one would think security would be priority… but again, physical access = pwned, etc.
Not quite the same, but funny: I recently unlocked an HDD from a car head unit to prove to a friend that it was only storing music ripped from its CD drive (and the associated minimal CD title database)… Toshiba master HDD password is 32 spaces. 😅
Oh shit hahaha that’s straight up disrespectful. Well yea I guess that makes sense but I just never thought to deep about it.
Yeah that is not really an “OMG” vulnerability as I can also get into that machine by booting it with a USB drive, or plugging it’s drove into my own machine.
That’s hyperbole. Such a system can be “hacked” by simply plugging in a usb-stick and booting from that instead, or dozens of other ways.
The only reason to use GRUB authentication I can think of would be in something like a kiosk.
… and yet some of the same people will readily copy-paste random shell scripts into their terminal without fully understanding them.
But a forum post said it would fix my issue.
I feel like there’s some truth to this!
If the posted answer was in a moderately active thread, you can generally assume it’s correct if there are no contradictory replies.
Let me open up my Linux bible and see if its malicious
…so, never put things in the terminal?
In fact, you should delete the terminal altogether. On a related note, powershell access is considered taboo in corporate environments by IT departments. When security audits are done, you lose a point if powershell can be used. It is in fact considered a hacking tool.
A friend of mine once downloaded something malicious to his Linux machine and wasn’t worried about it. Then some time later, while browsing his files from a Windows machine, saw it and was like, “hey, what’s this?” Oops.
He’s a tech savvy guy, so I’m guessing the fact he had downloaded it himself really let his guard down.
That’s why you don’t store your stool samples in the same fridge as your chocolate pudding. Malware goes into the vault.
This is were WINE comes handy /s
Virus running in wine: “WTF is this place. It’s familiar, but it’s all wrong!”
WannaCry: Platinium
https://appdb.winehq.org/objectManager.php?sClass=application&iId=18249
now im really tempted to try it, we have a decryptor now dont we?
inb4 decryptor: borked
What works
Encryption - Yes
GUI - Yes
What does not
SMB & Network replication does not always work, may require SMB network patch.
See: Misc Things to configure (Samba Shares)
Some Font rendering issues.
What was not tested
Decryption
Ransom Payment
Uh oh. And giving it “platinum” even though some stuff doesn’t work and basic features weren’t tested is bullshit. I demand a retraction!
Removed by mod
Why? You don’t wanna know how well WannaCry runs via Wine? The site is perfectly harmless.
Removed by mod
But you do know what wine and winehq is, right?
It’s just to WineHQ’s AppDb, it just describes how well stuff works with Wine. It’s similar to the newer ProtonDB. Someone tested the WannaCry/WannaCrypt malware with Wine for the hell of it.
It’s just an entry in Wine’s AppDB, where they keep track of how well apps run on wine. Like ProtonDB, but for general applications.
Removed by mod
Jesus, the downvotes! Well, I thought it was funny! 😂
Removed by mod
No maintainers yet. Any volunteers?
WannaCry is believed to use the EternalBlue exploit, which was developed by the U.S. National Security Agency (NSA)to attack computers running Microsoft Windows operating systems.
Hehe
Modern viruses check the os before deciding which type of file to send your way.
This is why you use a user agent switcher to lie about being windows. It’s a form of anti malware!
Except websites can tell what base OS you run using browser fingerprinting. It os impossible to lie aboit your OS because of the differences in platforms.
You can lie about your fingerprint very much in fact it is the default on librewolf
You can lie, but that doesnt mean that a website cant still tell your base OS if they use JS platform fingerprinting. Arkenfox, the base config which Librewolf is based off of says the exact same thing. Go to CreepJS and see it get your platform regardless.
You sweet summer child I use noscript
Firstly there is no need to be condescending.
Secondly, do you block all JS? NoScript is not a silver bullet and doesnt stop fingerprinting, it is itself identified by the CreepJS test site. It may in this case reduce the chance of OS fingerprinting, but pure CSS methods exist as well.
Additionally, NoScript is laregly redundant with uBlock Origin since you can do everything that it offers, such as blocking 3rd party scripts/iframes/all, block fonts, block JS, and it is very granular.
Bottom line, you are fingerpintable.
No script offers more than just is blocking you can block certain elements fonts what all that. It is NOT redundant. And creepjs doesn’t even run without js which I don’t allow on non trusted websites. Also yeah sorry I wasn’t trying to be condescending.
Generally browser fingerprinting is used to identify individual browser sessions across IP addresses. This mostly takes into account reported features and capabilities of the browser and OS to the website. Fingerprinting isn’t looking for specific info your browser reports, it’s taking it all and hashing it to get a unique id specific to the browser. Because it’s hashed, it can’t be reversed to identify the OS from the hash.
Sure a malicious website could Ignore the user agent and probe for some hardware capabilities that are specific to Linux, but that would be a lot of effort to probe various things which are set differently across all different browsers. I can’t speak for bad actors, but I wouldn’t spend the effort to check if the user agent is spoofed, if 95% of the time it’s accurate to get the OS type.